Step by Step Walkthrough Creating an Ribbon SBC SWe Lite VM on Azure and fully Deploying it with Teams Direct Routing
In the following series of articles, I will demonstrate how I have created a fully working Ribbon SBC VM (SBC SWe Lite) on Azure. I will also show how to integrate it with Teams Direct Routing and SIP Trunk
Such setup can be used to fully test and practice:
- Configuring Teams Direct Routing with Ribbon SBC
- Configuring Ribbon SBC
- Integrating a SIP Trunk with Ribbon SBC
Also can be used to demonstrate a proof of concept
Or you can even use it as a production. It is a fully working setup
Some of the advantages of such a setup:
- You don’t need to have a hardware SBC
- You don’t need to have your own Public IP to have integration with Direct Routing
- You don’t need to set up a firewall and other network equipment
- You can easily have integration with any SIP Trunk
The following are the links to the articles:
Part 3: Adding a Domain to Microsoft 365 – Jay’s Lab (jayslab.online)
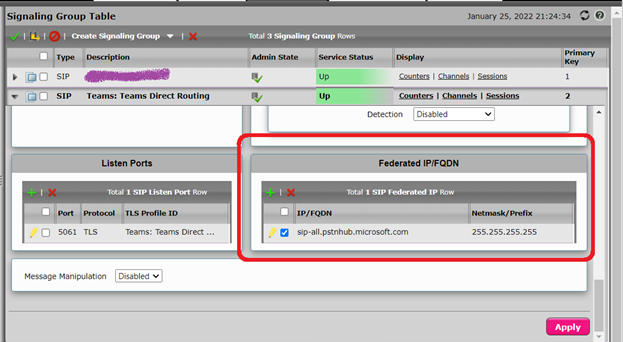
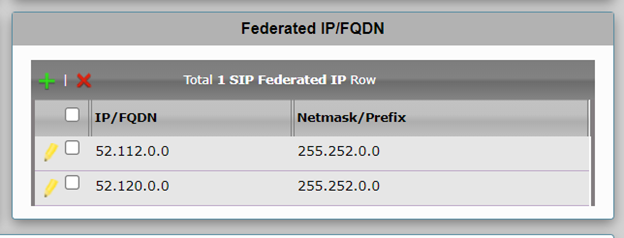
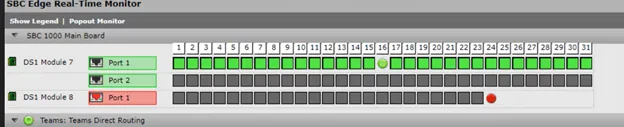
Part 5: Connecting the SBC SWe Lite to Teams Direct Routing – Jay’s Lab (jayslab.online)
Part 6: Changing the Host Name and Domain Name of SBC – Jay’s Lab (jayslab.online)
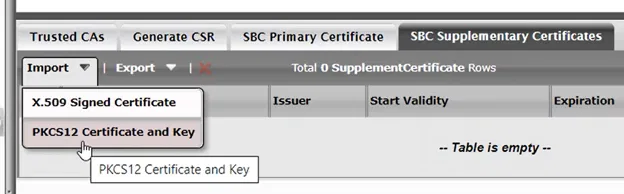
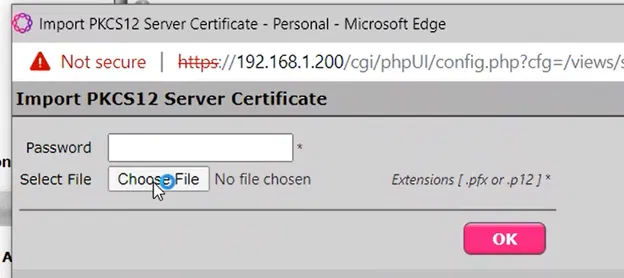
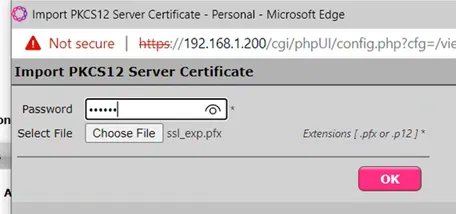
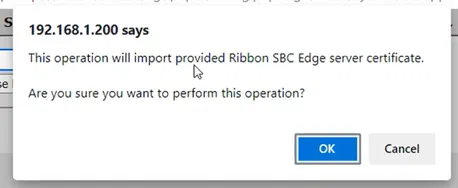
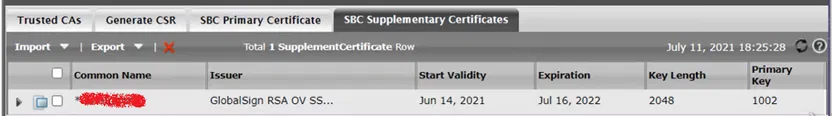
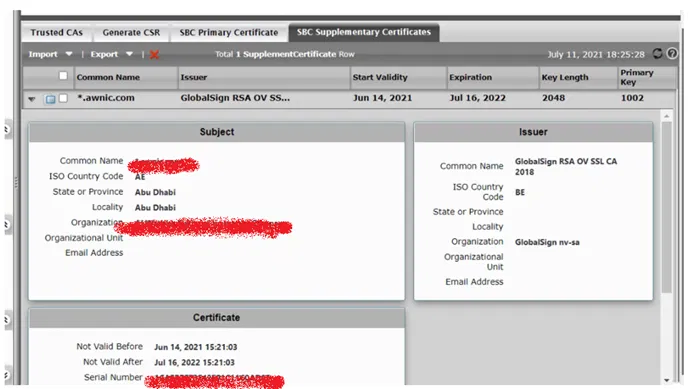
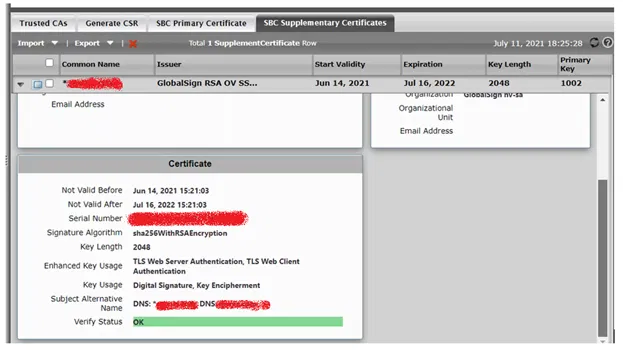
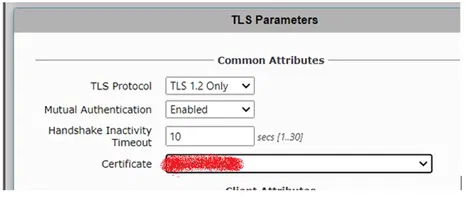
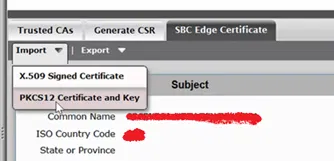
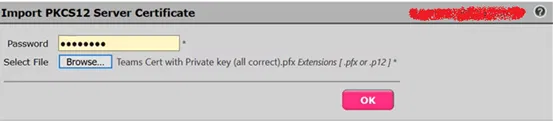
Part 7: Installing Certificates on the SBC – Jay’s Lab (jayslab.online)
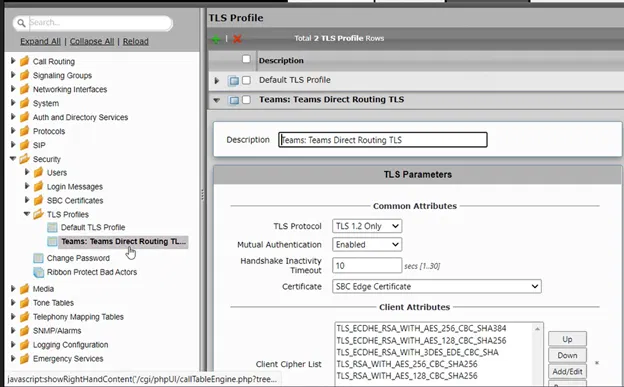
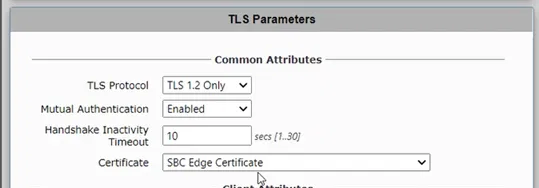
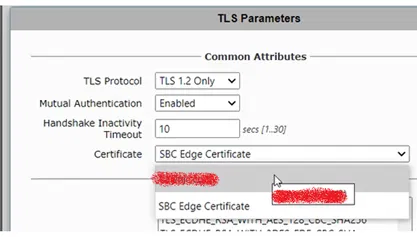
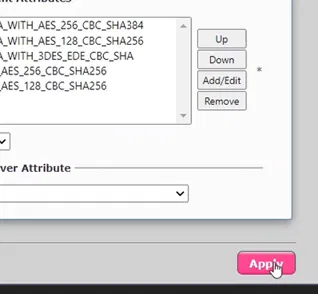
Part 8: Running Easy Config Wizard – Jay’s Lab (jayslab.online)
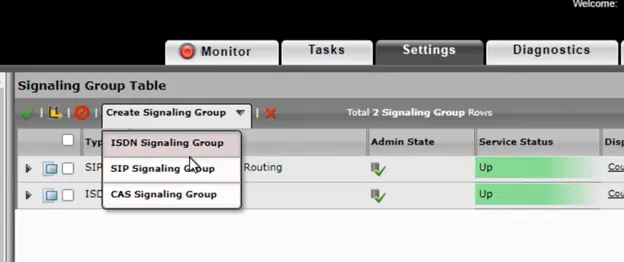
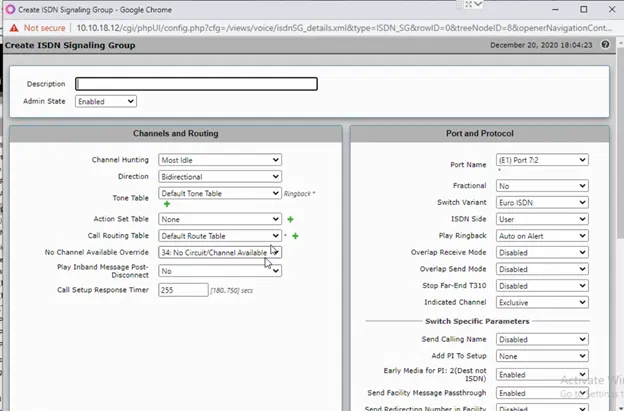
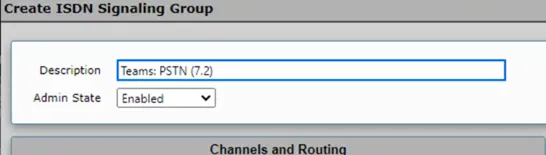
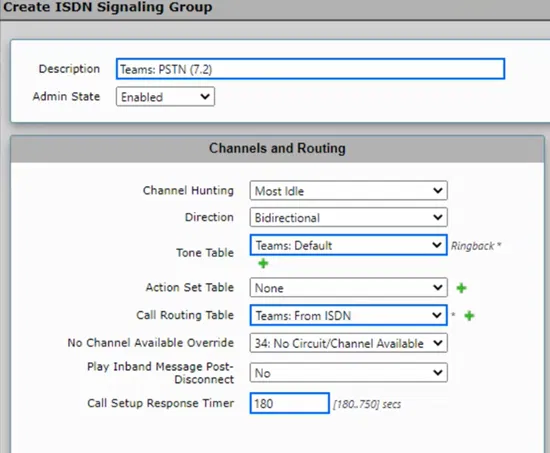
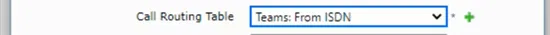
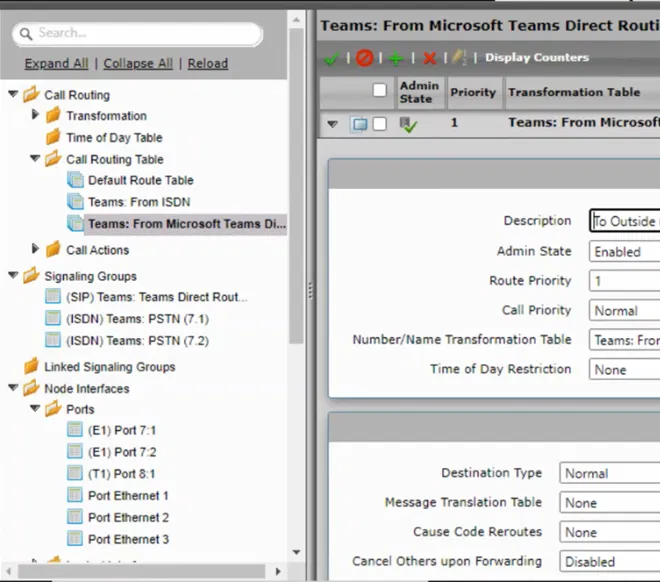
Part 9: Teams Direct Routing Call Routing – Jay’s Lab (jayslab.online)
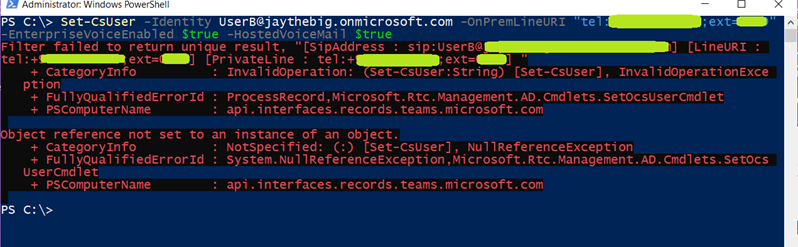
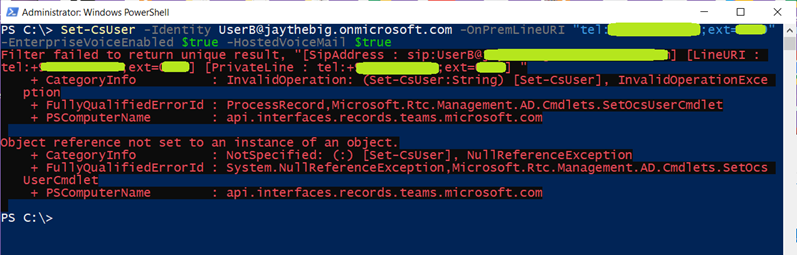
Part 10: Enable users for Direct Routing, voice, and voicemail – Jay’s Lab (jayslab.online)
Part 11: Testing Outgoing and Incoming Calls – Jay’s Lab (jayslab.online)